What are the four key cyber functions?
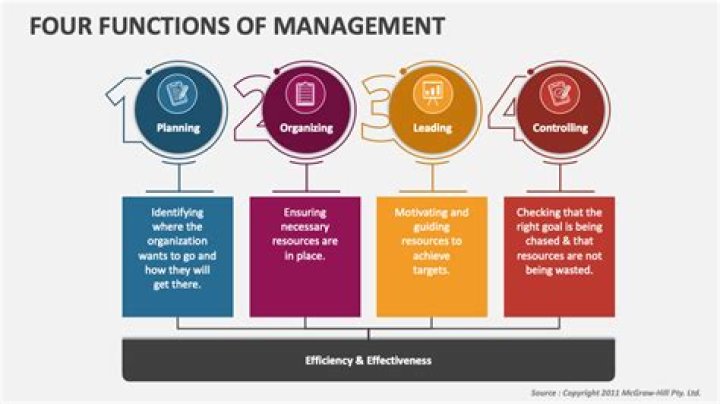
The third chapter of the primer looks at the four cyber operations roles: defensive cyber operations; cyber intelligence, surveillance and reconnaissance; offensive cyber operations; and cyber operational preparation of the environment.
What are the 4 principles of cybersecurity?
The purpose of the cyber security principles is to provide strategic guidance on how an organisation can protect their systems and data from cyber threats. These cyber security principles are grouped into four key activities: govern, protect, detect and respond.What are 4 cyber domains?
Collier et al., (2013) divided cybersecurity into four domains: the physical domain (hardware and software); the information domain (confidentiality, integrity and availability of information); the cognitive domain (how information is perceived and analyzed); and the social domain (attention to ethics, social norms and ...What are cybersecurity functions?
This learning module takes a deeper look at the Cybersecurity Framework's five Functions: Identify, Protect, Detect, Respond, and Recover.What are four types of cyber threat intelligence any four?
Supported the consumption of threat intelligence, it's divided into four differing types. they're specifically strategic threat intelligence , tactical threat intelligence , operational threat intelligence , and technical threat intelligence.Cyber Security In 7 Minutes | What Is Cyber Security: How It Works? | Cyber Security | Simplilearn
What are the three levels of cyber intelligence?
We can categorize and divide Cyber Threat Intelligence into three levels: strategic, tactical, and operational.
- Strategic CTI. It is non-technical and meant to shed light on trends and motivations affecting the threat landscape. ...
- Tactical CTI. Helps identify the how and where of attacks. ...
- Operational CTI.
What is the most common cyber threat?
Top 10 common types of cyber security attacks
- Malware.
- Phishing.
- Man-in-the-Middle (MitM) Attacks.
- Denial-of-Service (DOS) Attack.
- SQL Injections.
- Zero-day Exploit.
- Password Attack.
- Cross-site Scripting.
What are the 5 great functions of cybersecurity?
Here, we'll be diving into the Framework Core and the five core functions: Identify, Protect, Detect, Respond, and Recover. NIST defines the framework core on its official website as a set of cybersecurity activities, desired outcomes, and applicable informative references common across critical infrastructure sectors.What are the 5 types of cyber security?
Cybersecurity can be categorized into five distinct types:
- Critical infrastructure security.
- Application security.
- Network security.
- Cloud security.
- Internet of Things (IoT) security.
What are the 5 stages of the cybersecurity lifecycle?
In this article, we'll explain how to create a 5-phase cybersecurity lifecycle framework that can holistically improve your organization's security posture.
- Identify: Assess the security risk. ...
- Protect: Implement security measures. ...
- Detect: Monitor threats proactively. ...
- Respond: Create a response plan.
What are the four domains that a laboratory security program should follow?
The basic requirements are:
- Control Access - Restrict labs to authorized personnel only.
- Maintain Inventory - Know where and how much hazardous materials are in the lab.
- Reporting - Unaccounted loss and annual inventory.
- Training - all lab staff need to know the security procedures and why they are important.
What are the elements of cyber security?
Different Elements of Cybersecurity:
- Application security.
- Information security.
- Disaster Recovery Planning.
- Network Security.
- End-user Security.
- Operational Security.
What are cyber domains?
Cyber Domain - A global domain within the information environment consisting of the interdependent networks of information. technology infrastructures and resident data, including the Internet, telecommunications networks, computer systems, and. embedded processors and controllers.What is cyber security policy and explain any four types of cyber security policies?
Security policies are a formal set of rules which is issued by an organization to ensure that the user who are authorized to access company technology and information assets comply with rules and guidelines related to the security of information.What are the three main categories of security?
These include management security, operational security, and physical security controls.What are the steps to cyber security?
10 steps to cyber security
- Risk management regime. Assess the risks to your organisation's information and systems by embedding an appropriate risk management regime. ...
- Secure configuration. ...
- Network security. ...
- Managing user privileges. ...
- User education and awareness. ...
- Incident management. ...
- Malware prevention. ...
- Monitoring.
What are the 5 pillars of NIST?
The 5 pillars of the NIST framework consist of:
- Identify: Identify types of threats and all assets potentially at risk.
- Protect: Analyse how to best safeguard all identified assets.
- Detect: Define how threats against assets will be detected.
- Respond: Outline key measures to respond to detected threats.
What is the identify function in NIST?
The NIST Cybersecurity Identify Function sets the foundation for your Framework implementation project. It helps you to develop an organizational understanding of what you need to do to manage your district's cybersecurity risk to systems, people, assets, data, and capabilities.What is the key objective of the NIST Cybersecurity Framework?
The objective of the NIST Cybersecurity Framework is to identify “a prioritized, flexible, repeatable, performance-based, and cost-effective approach” to keeping data secure.What are the three 3 types of cyber threats?
Not all cyber attacks are created equal and in this post we hope to shed some light on the "Big 3" types of cyber attacks, malware, ransomware, and phishing attacks.What are the 3 threats to information security?
Information Security threats can be many like Software attacks, theft of intellectual property, identity theft, theft of equipment or information, sabotage, and information extortion.What are the types of attacks?
Types of Cyber Attacks
- Malware Attack. This is one of the most common types of cyberattacks. ...
- Phishing Attack. Phishing attacks are one of the most prominent widespread types of cyberattacks. ...
- Password Attack. ...
- Man-in-the-Middle Attack. ...
- SQL Injection Attack. ...
- Denial-of-Service Attack. ...
- Insider Threat. ...
- Cryptojacking.